Certain insurance firms in the market are starting to view Managed Detection and Response (MDR) as the new checkbox equivalent of Multi-factor Authentication (MFA), offering reduced premiums and serving as compliance benchmarks for a company’s commitment to enhancing its risk management culture. Could this trend signify the next phase of evolution in business compliance? Here at CSP, we believe so!
That’s why we’ve dedicated considerable effort over the past few years, starting with the early launch of Microsoft Sentinel in 2019, to craft a tailored and cost-effective solution, designed with the SME sector in mind. The enthusiastic feedback we’ve received from many of our clients regarding the enhancements we’ve made to their cybersecurity stance, compliance adherence, and early threat detection capabilities has truly fuelled our momentum and affirmed that we’re on the right track!
In Australia, businesses are confronted with increasingly sophisticated cyber threats targeting their most valuable assets: finances, data, and reputation. Critical business components such as bank accounts, email systems, and various devices, including computers and mobile devices, are all susceptible to compromise.
The Australian Signals Directorate’s (ASD’s)Australian Cyber Security Centre (ACSC) recently released a report on the cyber security of Australian Small Businesses. Some of the stats are telling:
- – Australian Cyber Security Centre (ACSC) receives 1 report every 10 minutes
- – Estimated annual losses to cybersecurity are $300M
- – 1 in 5 are unaware of the term Phishing
- – Half of SMBs reported they spend less than $500 oncyber security per year.
- – Only 20 percent are properly equipped with cyberinsurance.
- – Average cost of cybercrime has risen from $39,000 to $46,000.
These statistics serve as a source of encouragement for us at CSP as we remain committed to ensuring that our Managed Detection and Response (MDR) surpasses mere detection capabilities. At the heart of our approach lies a philosophy of nurturing partnerships through knowledge sharing and elevating your security posture in a rapidly evolving landscape.
Traditionally, Security Operation Centers (SOCs) would offer recommendations, leaving IT departments, Chief Information Security Officers (CISOs), CEO’s, and IT sysadmins grappling with the implementation of complex technical changes. We frequently encounter organizations puzzled by questions such as:
- – What exactly is Zero Trust?
- – How do we implement Conditional Access policies to deal with a semi-remote workforce?
- – What does effective device management entail?
- – How can we identify all our assets and assess associated risks?
- – What is our risk profile?
- – How do we consolidate disparate cybersecurity solutions that are costing us a fortune?
Recognizing the need for clarity and guidance, we have built answers to these queries into our service offerings. This approach sets us apart as a truly unique service provider.
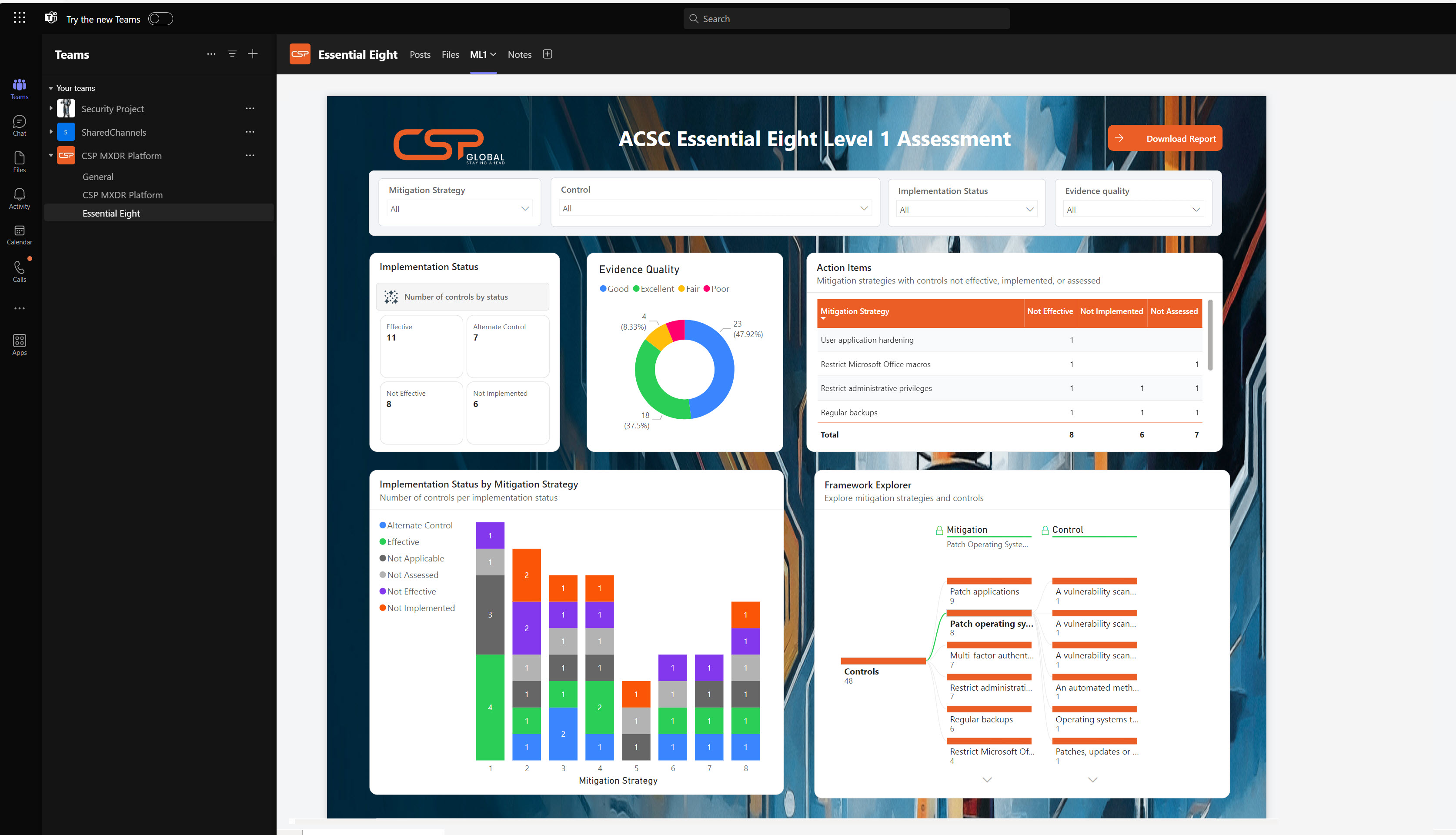
Not only do we deploy a Microsoft Teams integrated platform that provides full visibility into our services, showcasing our incident management, early warning detection capabilities, and Threat Intelligence, but we also address digital hygiene and compliance questions that SMEs have struggled to navigate.
“Outsourcing may lead to gaps in the owner’s cybersecurity knowledge about which security measures are being implemented to protect their business. Data shows that for many SMBs opting to outsource, their outsourced provider did not necessarily implement all of the Essential Eight”
– ACSC Small Business report
As ACSC alludes to in their report – some service providers have not followed through on their promises, especially when it comes to Essential Eight alignment, something we’ve witnessed first-hand. At CSP, we implement all eight mitigation strategies as well as present evidence in a comprehensive report, and best of all, it’s built directly into your platform. When service providers claim to align with ES8 the best proof is in the pudding. Evidence should be part of any compliance effort. You do not want to find out these controls do not exist while lodging an insurance claim.
For additional insurance and business continuity, we’ve cultivated relationships with trusted insurance brokers who can enlighten SMEs on the benefits of cybersecurity policies in today’s landscape. By aligning with a managed cybersecurity service provider like us, which assists with technology aspects covered in insurance questionnaires, SMEs can realize significant cost savings on premiums—a testament to our commitment to going above and beyond.
This year, we’re thrilled to unveil our forthcoming interactive guided tours and our Lighthouse MXDR trial. These initiatives will empower organizations with a comprehensive understanding of their operational activities and provide actionable insights on reducing costs while maintaining a robust cybersecurity posture. We look forward to announcing the release on our website soon.
If you want to find out more book a free demo with us here.

